The Hesitation Gap
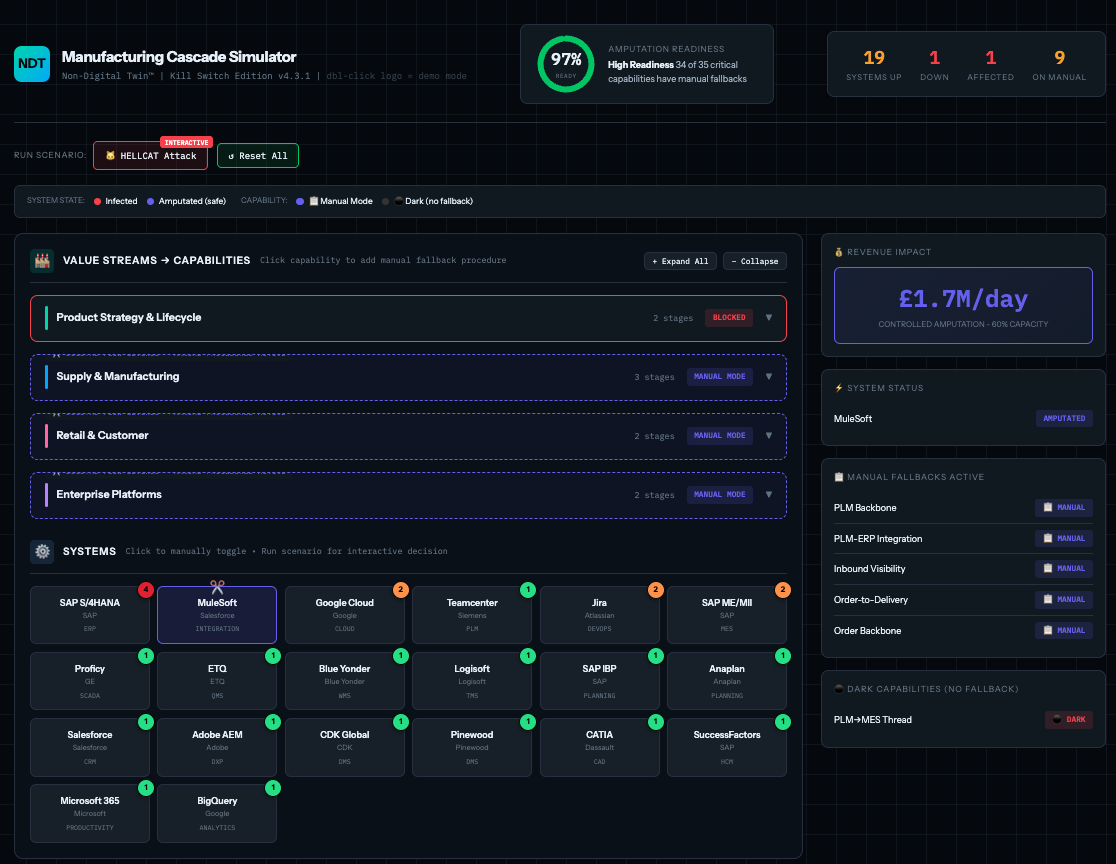
When ransomware hits, the first critical decision is: shut down everything immediately, or try to contain? Organisations that hesitate — because they don't know if they can survive without their digital systems — give the attacker time to spread laterally. By the time they decide to shut down, the attacker has moved from one system to twenty.
The hesitation gap isn't a technology problem. It's a confidence problem. Organisations with documented manual fallback procedures can make the shutdown decision immediately. They know they can operate — imperfectly, slowly, but they can operate — without IT systems. That confidence transforms cyber resilience from a technology investment into an organisational capability.
The Cold Read
We don't ask for "time to learn your business." We arrive knowing it. Before any contract is signed, we hand you a Financial Tension Map — a one-page analysis based entirely on public data: annual reports, audited filings, investor decks, earnings calls. Every number traced to source. No hallucination. Fully auditable.
The Cold Read shows your stated strategy alongside your actual capital allocation. Where there's a disconnect — you say you're pivoting to digital services but your capex still heavily favours legacy products — that's either a timing issue or a strategy-execution gap. Either way, it's visible from your public filings. If we can see it, so can anyone targeting you.
If the Cold Read is wrong, don't hire us. If it's right — and it will be — we've just demonstrated why we're different from every consultant who asks you to explain your own business before they can help.
The promise: if this map isn't 90% accurate to your internal reality, don't hire us. Most consultants ask "tell me your problems." We show you the ones you haven't noticed.
What the Twin Contains
Capability-by-capability manual procedures. What do your people actually do when systems are dark? Not what the BCP document says — what they actually do. We ask them directly using Clean Language methodology: "what happens to X when the system isn't available?" The answers often surprise leadership.
Quantified recovery estimates. Not "we'll be back in 72 hours" as a guess. "72 hours ±12 hours at 90% confidence. Q4 extends to 120 hours due to seasonal volume. Revenue impact is £180K/day. Maximum exposure is £900K." Quantified uncertainty that insurers can actually price against.
The rationalisation dividend. When we ask "if systems went dark, what would you do?", people often say "honestly, we'd just use the spreadsheet" or "we'd skip that step." One client discovered 34 applications that nobody could explain needing in a recovery scenario. Annual cost of that list: £2.4M. The Twin isn't just resilience documentation — it's rationalisation evidence.
Why IPFS Changes Everything
Traditional business continuity documentation sits on the same network the attacker just compromised. Binders in a warehouse. SharePoint sites. Confluence pages. All reachable. All encryptable. All deniable.
The Non-Digital Twin is stored on IPFS — content-addressed, distributed, cryptographically immutable. The address IS the hash of the content. Change one byte, different address. This transforms documentation from hearsay to evidence. When the insurer asks "what documentation existed pre-incident, and can you prove it?" — the CID resolves to exactly what you had, timestamped and tamper-proof.
Insurance premium reduction of 15–20% pays for the ongoing maintenance. The implementation pays back in 3–4 years — before counting avoided losses or rationalisation savings. The product funds itself.
The Board Paper
Companies Act 2006, Section 174: directors must exercise reasonable care, skill, and diligence. A reasonably diligent director, knowing that cyber attacks are foreseeable and material, that insurance claims can be denied for documentation failures, and that business interruption can be existential — would conclude that adequate preparation is necessary.
The question for every board: "If we suffer a cyber attack tomorrow and the business fails because our documentation was inadequate, can directors personally demonstrate they exercised reasonable care?" If the answer isn't "yes, here's the evidence" — that's the liability gap the Twin fills.
Commercial Model
Discovery Only: £5–10K. AI-generated capability map plus tension analysis. Two weeks. This is the Cold Read — you see what we can do before committing further.
Full Diagnostic: £25–40K. Survey, analysis, conversation map, quantified uncertainty. Four to six weeks.
Complete Twin: £50–75K. Everything compressed, stored on IPFS, maintainable. Eight to ten weeks.
Maintenance: £15–20K/year. Quarterly refresh plus daily deltas plus annual full refresh. Ongoing.